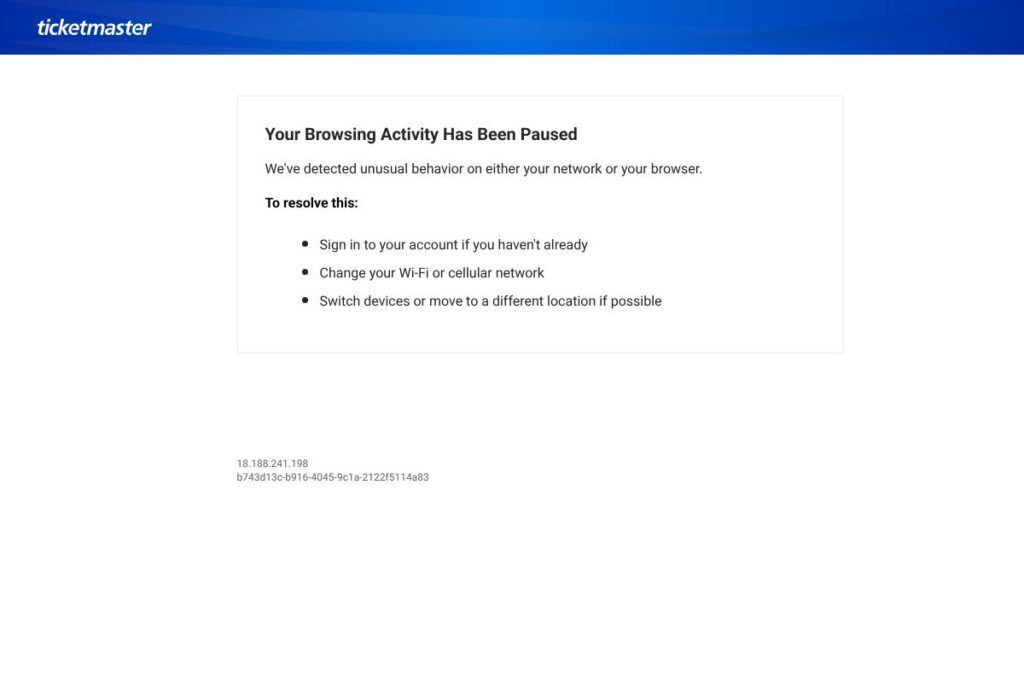
What is Let’s Get Your Identity Verified?
Let’s Get Your Identity Verified is a verification checkpoint shown to visitors when a site detects unusual network traffic or browser behavior. The page prompts the user to sign in, switch networks or devices, or move locations to reduce risk and restore normal browsing.
This type of checkpoint sits between the user and a protected web application, pausing browsing while the host collects session identifiers and contextual signals. It is comparable to challenge pages and bot mitigation tools from providers like Cloudflare Bot Management and Google reCAPTCHA Enterprise, although those services are broader security platforms rather than a single verification prompt.
What this page does well is present a clear, actionable path for end users to recover access while allowing operators to log IPs, session IDs, and diagnostic tokens for investigation. It is most useful for site administrators who need an on-demand verification layer to handle suspicious or automated traffic without immediately blocking legitimate users.
How Let’s Get Your Identity Verified Works
When the hosting site detects anomalies from a browser or IP address fingerprint, it intercepts the session and displays the verification prompt. The page records identifiers such as the visitor IP and a session token to link any subsequent sign-in or remediation steps to the original event.
Common remediation flows include asking the user to sign in to an existing account, switching to another network, or using a different device. The hosting site typically uses server-side rules, CDN controls, or a bot management service to determine when to trigger the checkpoint and how to proceed after verification.
Administrators can configure these checkpoints as part of an overall access control workflow. That configuration often ties into rate limits, challenge-response engines, or risk scoring systems that decide whether to allow, challenge, or block the session.
What does Let’s Get Your Identity Verified do?
This verification prompt focuses on short-term access remediation and identity confirmation. Core capabilities include capturing an IP address and session token, instructing users on immediate steps to resolve the block, and providing operators with diagnostic context for follow-up.
Key functionality includes:
Browser and network detection
The page identifies anomalies in browser fingerprinting, headers, or request patterns and logs the visitor IP for investigation. This helps operators separate legitimate users from automated or risky traffic patterns and supports forensic analysis.
Account sign-in prompt
Users are asked to sign in if they have an account, which is a straightforward way to confirm identity and restore access. Signed-in sessions can be associated with the recorded session token to validate the remediation action.
Device and location guidance
The checkpoint suggests switching networks, moving to a different location, or changing devices when network-level signals show unusual behavior. These suggestions reduce false positives for legitimate mobile or roaming users.
Session and diagnostic token capture
A nonce or diagnostic identifier is recorded with the visitor context to allow operators to trace the event in server logs or security dashboards. That token is useful when escalating to support or security teams.
Integration with bot and risk engines
The prompt is typically an output of a larger risk decisioning system and can be integrated with bot management, rate limiting, or IP reputation services. Integration allows automated escalation to blocking or allowlisting after verification.
With these features, the biggest benefit is rapid, simple remediation for interrupted sessions while preserving detailed diagnostic context for administrators.
Let’s Get Your Identity Verified Pricing
This verification prompt does not publish a dedicated pricing page; it is generally offered as a feature within a broader security or CDN platform and pricing is handled by that parent product. For current cost information and licensing options, consult the service provider’s main site or contact their sales team for details.
What is Let’s Get Your Identity Verified Used For?
Site operators use this verification checkpoint to pause potentially risky sessions while giving legitimate users a path to restore access. It is useful for preventing automated scraping, mitigating credential stuffing attempts, and reducing false positives that would otherwise cause outright blocks.
It is most appropriate for businesses that need a lightweight, user-facing control to handle anomalous traffic without immediate account suspension. Security teams combine it with logging and alerting so incidents can be investigated and remediated efficiently.
Pros and Cons of Let’s Get Your Identity Verified
Pros
- Simple remediation flow: The prompt gives clear next steps for users, such as signing in or switching networks, which helps reduce user frustration and support tickets.
- Diagnostic context captured: IP addresses and session tokens are recorded, enabling security teams to investigate incidents and correlate events across logs.
- Flexible deployment model: Checkpoints can be inserted at the CDN, web server, or application layer and tied to existing bot or risk engines for automated handling.
Cons
- User friction for legitimate users: Some genuine visitors may be blocked or paused and need to follow extra steps to continue, which can affect conversion rates.
- Limited standalone functionality: The prompt alone is not a full bot management or identity verification platform; it is typically one component of a larger security stack.
- Dependence on accurate risk signals: If the underlying detection rules are too aggressive, the checkpoint will trigger frequently and generate false positives.
Does Let’s Get Your Identity Verified Offer a Free Trial?
Let’s Get Your Identity Verified is not typically a standalone product with a free trial. It is usually bundled into a larger security or CDN offering, so trial availability depends on that parent product; check the provider’s account or contact channels for trial or demo access.
Let’s Get Your Identity Verified API and Integrations
This verification prompt is commonly surfaced through a platform integration rather than a public API of its own. Operators typically enable it through CDN or bot management controls in the host platform, and associated logs feed into existing observability or SIEM tools.
For examples of how platforms expose similar functionality, see Cloudflare Bot Management documentation and Google reCAPTCHA Enterprise integration guides for implementation patterns and webhook usage.
10 Let’s Get Your Identity Verified alternatives
Paid alternatives to Let’s Get Your Identity Verified
- Cloudflare Bot Management — A commercial bot mitigation suite that includes challenge pages, fingerprinting, and managed rulesets to reduce automated traffic.
- Akamai Bot Manager — Enterprise-grade bot detection and response capabilities integrated with Akamai’s CDN and security portfolio.
- PerimeterX Bot Defender — Behavioral-based bot detection and mitigation focused on protecting login, checkout, and content pages.
- Imperva Bot Management — Offers managed bot protection and challenge workflows with analytics and rule tuning.
- Google reCAPTCHA Enterprise — Risk assessment and challenge handling with a managed API for protecting high-value pages.
- Distil Networks — Bot detection platform that identifies and blocks automated traffic with challenge-response options.
- ShieldSquare — Behavioral detection for bots with challenge and mitigation workflows for e-commerce and media sites.
Open source alternatives to Let’s Get Your Identity Verified
- ModSecurity — An open source web application firewall that can be configured to present challenges or block suspicious traffic at the web server level.
- Fail2ban — A log-parsing tool that can react to suspicious activity by blocking IPs at the firewall layer, useful for simple automated mitigation.
- OWASP Core Rule Set (CRS) — Rules for ModSecurity and other WAFs that help detect common attack patterns and reduce malicious requests.
- Keycloak — An open source identity and access management solution that can be integrated to require authentication before granting access.
- PrivacyIDEA — Open source multi-factor authentication and verification framework that can be used to require identity confirmation for risky sessions.
Frequently asked questions about Let’s Get Your Identity Verified
What is Let’s Get Your Identity Verified used for?
Let’s Get Your Identity Verified is used to pause browsing and require verification when a site detects unusual network or browser behavior. It gives users steps to regain access while capturing context for administrators to investigate.
Does Let’s Get Your Identity Verified store IP addresses?
Yes, the verification flow typically records the visitor IP address and a session token for diagnostics. Those identifiers help map the event to server logs and security tools for follow-up.
Can Let’s Get Your Identity Verified be customized for my site?
Customization depends on the hosting platform that provides the checkpoint. Administrators usually configure trigger thresholds, challenge messaging, and integration with authentication systems via the parent service’s controls.
How does Let’s Get Your Identity Verified compare with reCAPTCHA?
Let’s Get Your Identity Verified is a site-level checkpoint focused on remediation, while reCAPTCHA provides risk scoring and challenge widgets for bot detection. Both can be used together as part of a layered defense strategy.
Is Let’s Get Your Identity Verified suitable for e-commerce checkout pages?
It can be used on checkout pages but should be applied carefully to avoid disrupting conversions. Use targeted triggers and user-friendly remediation steps to minimize checkout abandonment.
Final verdict: Let’s Get Your Identity Verified
This verification prompt serves as a practical, straightforward control to handle suspicious browser or network behavior while giving legitimate users a clear path to regain access. It excels at capturing diagnostic context such as IP addresses and session tokens and at providing immediate, user-focused remediation steps.
Compared with a full bot management product like Cloudflare Bot Management, this checkpoint is narrower in scope and usually bundled into a larger platform. Cloudflare publishes tiered pricing for its bot protection and provides advanced analytics and automated rule tuning, while this checkpoint itself does not have a public pricing page and is priced according to the parent service. For operators who need granular bot management and analytics, a dedicated bot mitigation vendor may be a better fit; for teams seeking a lightweight, user-facing verification step, this prompt is an effective addition to an existing security stack.